
WP BAC MAR 2024
WP Broken Access Control
Managed WordPress Security Report
Be informed about the latest WP Broken Access Control, identified and reported publicly. WP BAC MAR 2024 is a +29% INCREASE compared to previous month. Consider for your online safety, a managed WP/Woo security AUDIT, – OR – switching with a TOP10LIST alternative WP Security Plugin – OR – Hire us for your recurrent needs of managed WordPress Security and managed WooCommerce Security. The following cases made headlines PUBLICLY just last month in the WP Broken Access Control category:
WHO needs managed WP security? EVERYBODY!
Today's reality needs a Web Application Firewall (WAF) plus an Intrusion Prevention System (IPS) to mitigate "gazillion" different threats in your WordPress. Get your WP BAC MAR 2024: WP Broken Access Control Patch Management.
| WP BAC & WordPress Broken Access Control reported in 2023: | 931 |
| WP BAC & WordPress Broken Access Control reported in 2024: | 213 |
WHO needs managed WP Maintenance? EVERYBODY!
Today’s reality requires daily clean-ups with database optimisations, weekly updates and upgrades for both free & premium modules, plus the occasional emergency changes when critical vulnerabilities are publicly disclosed without patches. Order WP BAC MAR 2024: WP Broken Access Control Patch Management.
BRIEF: WP Broken Access Control are critical security vulnerabilities in which attackers can perform any action (access, modify, delete) outside of WordPress or WooCommerce intended default user permissions (subscriber, customer, etc).
What is Broken Access Control?
A security threat, where intruders are able to gain access to unauthorised data. Broken access control is a failure on the OWN security to carry out and maintain pre-established user access policies. Bypassing intended permissions, intruders become able to reach sensitive information, modify and outright delete or download data, or perform business functions that you wouldn’t want them to perform. Like ordering a single product, paying and after confirmation tampering the saved cart ordered item numbers.
Broken access control vulnerabilities can have far-reaching consequences. Privileged data could be exposed, malware could be loaded to further attacks and destruction. Beyond the initial breach, companies face litigation, damage control, loss of market share and reputation, repair of compromised systems, and delays in deploying live improvements. With exploits and attacks more prevalent than ever, ensuring your system’s security is more important than ever.
What is Insecure Direct Object Reference (IDOR)?
Insecure direct object references (IDOR) are a type of access control vulnerability that arises when an application uses user-supplied input to access objects directly. It leads to access controls being circumvented. IDOR vulnerabilities are most commonly associated with reaching resources from database entries belonging to other users, files in the system, and more. This is caused by the fact that the application takes user supplied input and uses it to retrieve an object without performing sufficient authorisation checks.
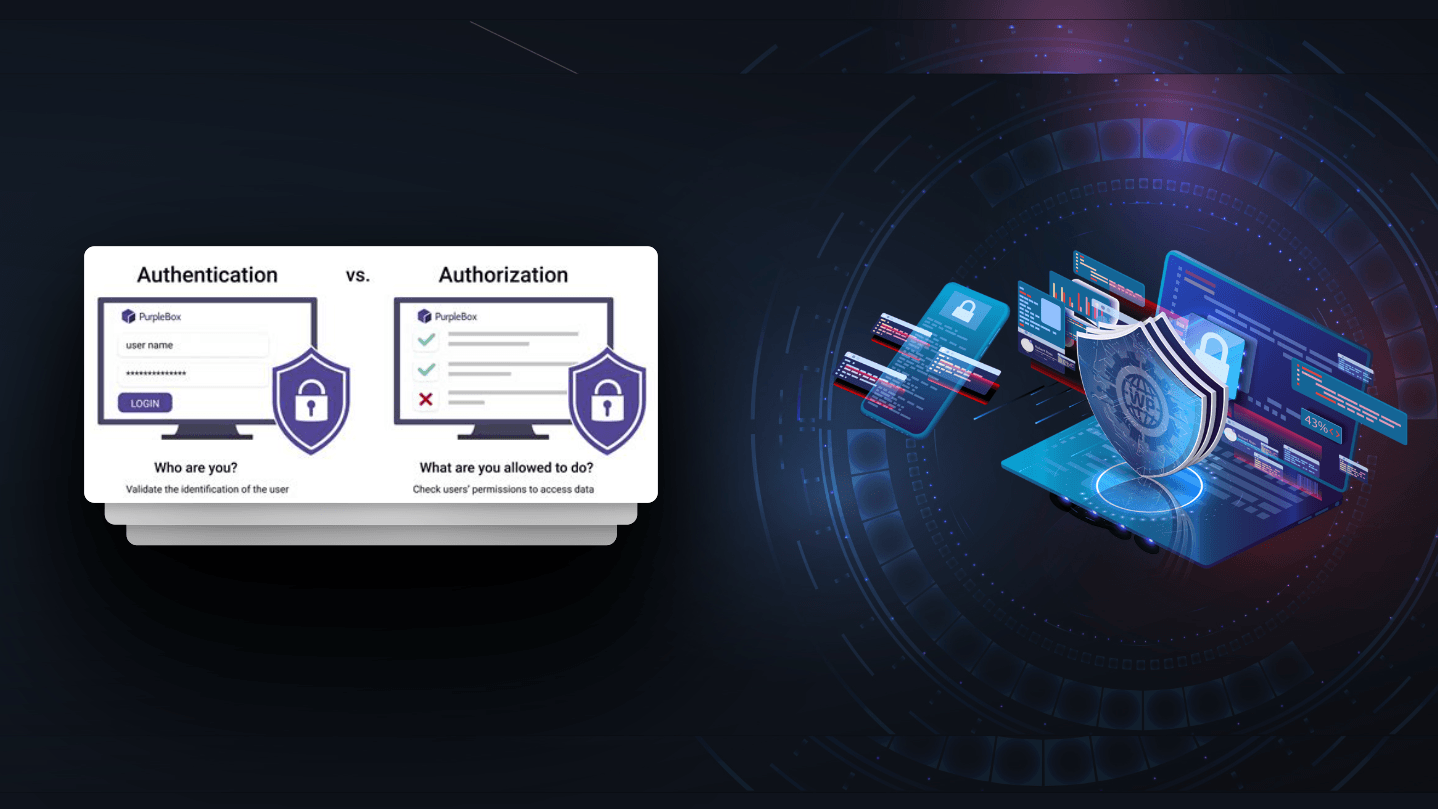
What is Missing Authorisation?
Assuming a user with a given identity, authorisation is the process of determining whether that user can access a given resource, based on the user's privileges and any permissions or other access-control specifications that apply to the resource. When access control checks are not applied, users are able to access data or perform actions that they should not be allowed to perform. This can lead to a wide range of problems, including sensitive and private information exposures, remote or arbitrary code execution.
What is Directory or Path Traversal?
Directory traversal (or file path traversal) is a security vulnerability that allows an attacker to read specific files on the server that is running inside your WordPress or WooCommerce. This might include plugin or theme code and data, credentials for back-end systems, 3rd party integrations, hosting environment details, or sensitive operating system files. In some cases, an attacker might be able to write into these files on the server, allowing them to modify application data or behaviour, and ultimately taking full control of the infrastructure.
Security is not a single-task job
Need managed WP Security and got no clue where to start? Hire an expert. Pay a coffee per week, its cheaper than 1 hour for a freelancer.
Not sure that our recurrent security offer is worthy of long-term consideration? Contact us today for a Broken Access Control audit! Decide after you compare RISK + IMPACT versus COST.
We’re passionate about helping you grow and make your impact
Continue being informed
Monthly vulnerability reports about WordPress and WooCommerce, plugins, themes.
Weekly inspiration, news and occasional with hand-picked deals. Unsubscribe anytime.


