XSS JUL 2022 - Cross-Site Scripting JUL 2022
Tailored WordPress Security Report
Be informed about the latest Cross-Site Scripting JUL 2022, identified and reported publicly. As these XSS JUL 2022 vulnerabilities have a severe negative impact on any WordPress Security, consider our security audit.
An estimated jaw-dropping 13.244.000+ active WordPress installations were susceptible to these attack types, considering only the publicly disclosed and available numbers. It is a significant +30.3% INCREASE compared to last month. The estimated number can increase by 20-25% with premium versions as they are private purchases.
Furthermore, the initial estimation can triple if we consider (1) the already patched versions BUT NOT UPDATED by owners, as the vulnerability remains active within their domain; and (2) the closed "uncounted" versions remain active on domains already running the plugins, as nobody is maintaining security. As these owners start changing their hosting provider (due to constant unexplained issues), they actively migrate these vulnerabilities behind new / protected areas, possibly exposing other clean WP to different attack types.
The following cases made headlines PUBLICLY in the XSS JUL 2022 category:
Hire security geeks to protect your WP/Woo from publicly reported cases of XSS JUL 2022 BEFORE IT’S TOO LATE! You will also protect your customers, your reputation and your online business!
- GTM4WP - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 600,000+
- Consider for your online vigilance, switching with a TOP10LIST alternative WP Monitoring Plugin - OR - Hire professionals for managed WP Monitoring.
- Rotating Posts - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 24, 2022 and is not available for download. This closure is temporary, pending a full review.
- Germanized for WooCommerce - Reflected Cross-Site Scripting (XSS)
- Active installations: 90.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- Automatic Domain Changer - Reflected Cross-Site Scripting (XSS)
- Active installations: 10.000+
- Consider for your online ranking, switching with a TOP10LIST alternative WP SEO Plugin - OR - Hire professionals for managed WP SEO.
- CURCY – Multi Currency for WooCommerce – The best free currency exchange plugin – Run smoothly on WooCommerce 6.x - Reflected Cross-Site Scripting (XSS)
- Active installations: 20.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- Video Conferencing with Zoom - Reflected Cross-Site Scripting (XSS)
- Active installations: 30.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Visualizer: Tables and Charts Manager for WordPress - Reflected Cross-Site Scripting (XSS)
- Active installations: 40.000+
- Popups, Welcome Bar, Optins and Lead Generation Plugin – Icegram - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 30.000+
- Easy SVG Support - Authenticated Stored Cross-Site Scripting (XSS) via SVG
- Active installations: 3.000+
- Consider for your loading time, switching with a TOP10LIST alternative WP Speed Plugin - OR - Hire professionals for managed WP Speed Up.
- New User Approve - Arbitrary Settings Update & Invitation Code Creation via Cross-Site Request Forgery (CSRF)
- New User Approve - Reflected Cross-Site Scripting (XSS)
- Active installations: 20.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Modern Events Calendar Lite - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of May 11, 2022 and is not available for download. This closure is permanent.
- WPMK Ajax Finder - Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 17, 2022 and is not available for download. This closure is temporary, pending a full review.
- Active Products Tables for WooCommerce. Professional products tables for WooCommerce store - Reflected Cross-Site Scripting (XSS)
- Active installations: 3.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- Mobile browser color select - Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of April 29, 2022 and is not available for download. This closure is temporary, pending a full review.
- Clean-Contact - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 27, 2022 and is not available for download. This closure is temporary, pending a full review.
- Add Post URL - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 27, 2022 and is not available for download. This closure is temporary, pending a full review.
- Consider for your online ranking, switching with a TOP10LIST alternative WP SEO Plugin - OR - Hire professionals for managed WP SEO.
- Flower Delivery by Florist One - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 100+
- Mihdan: No External Links - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of April 5, 2022 and is not available for download. Reason: Security Issue.
- Consider for your online ranking, switching with a TOP10LIST alternative WP SEO Plugin - OR - Hire professionals for managed WP SEO.
- Ultimate Member – User Profile, User Registration, Login & Membership Plugin - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 200.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Form – Contact Form - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 2, 2022 and is not available for download. This closure is temporary, pending a full review.
- Image Gallery – Grid Gallery - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 2, 2022 and is not available for download. This closure is temporary, pending a full review.
- NextCellent Gallery – NextGEN Legacy - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 1, 2022 and is not available for download. This closure is temporary, pending a full review.
- Site Offline or Coming Soon - Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 5, 2022 and is not available for download. This closure is temporary, pending a full review.
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- WordPress Security – Firewall, Malware Scanner, Secure Login and Backup - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 900+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Customizable WordPress Gallery Plugin – Modula Image Gallery - Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Malware Scanner - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 300+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- miniOrange's Google Authenticator – WordPress Two Factor Authentication (2FA , Two Factor, OTP SMS and Email) | Passwordless login - Authenticated Stored Cross-Site Scripting (XSS)
- miniOrange's Google Authenticator – WordPress Two Factor Authentication (2FA , Two Factor, OTP SMS and Email) | Passwordless login - Reflected Cross-Site Scripting (XSS)
- Active installations: 20.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Nested Pages - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 90.000+
- Limit Login Attempts - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 3.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Ninja Forms Contact Form – The Drag and Drop Form Builder for WordPress - Authenticated Stored Cross-Site Scripting (XSS)
- Ninja Forms Contact Form – The Drag and Drop Form Builder for WordPress - Unauthenticated PHP Object Injection
- Active installations: 1+ million
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- WooCommerce Menu Cart - Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- WP Menu Cart - Reflected Cross-Site Scripting (XSS)
- Active installations: 9.000+
- WooCommerce PDF Invoices & Packing Slips - Reflected Cross-Site Scripting (XSS)
- Active installations: 300.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- 404 to 301 – Redirect, Log and Notify 404 Errors - Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Consider for your online ranking, switching with a TOP10LIST alternative WP SEO Plugin - OR - Hire professionals for managed WP SEO.
- Gravity PDF - Reflected Cross-Site Scripting (XSS)
- Active installations: 50.000+
- Consider for your loading time, switching with a TOP10LIST alternative WP Speed Plugin - OR - Hire professionals for managed WP Speed Up.
- Export any WordPress data to XML/CSV - Reflected Cross-Site Scripting (XSS)
- Active installations: 90.000+
- Consider for your online disaster recovery, switching with a TOP10LIST alternative WP Backup Plugin - OR - Hire professionals for managed WP Backup.
- SAML Single Sign On – SAML SSO Login - Reflected Cross-Site Scripting (XSS)
- Active installations: 9.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Download Manager - Reflected Cross-Site Scripting (XSS)
- Download Manager - Authenticated Stored Cross-Site Scripting (XSS)
- Download Manager - Unauthenticated Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Copify - Cross-Site Request Forgery (CSRF) to Cross-Site Scripting (XSS)
- This plugin has been closed as of May 27, 2022 and is not available for download. This closure is temporary, pending a full review.
- Gallery Bank – WordPress Photo Gallery Plugin - Authenticated Stored Cross-Site Scripting (XSS) via Gallery Description
- Gallery Bank – WordPress Photo Gallery Plugin - Authenticated Stored Cross-Site Scripting (XSS) via Media Upload Module
- This plugin has been closed as of December 9, 2021 and is not available for download. Reason: Security Issue.
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- ToolBar to Share - Cross-Site Request Forgery (CSRF) to Cross-Site Scripting (XSS)
- This plugin has been closed as of May 31, 2022 and is not available for download. This closure is temporary, pending a full review.
- Mitsol Social Post Feed - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of March 14, 2022 and is not available for download. Reason: Security Issue.
- Grow Social - Reflected Cross-Site Scripting (XSS)
- Active installations: 70.000+
- Elementor Website Builder - Unauthenticated DOM-based Reflected Cross-Site Scripting (XSS)
- Active installations: 5+ million
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Spectra – WordPress Gutenberg Blocks - Reflected Cross-Site Scripting (XSS)
- Active installations: 300.000+
- WP Contact Slider - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 20.000+
- Clearfy Cache – WordPress optimization plugin, Minify HTML, CSS & JS, Defer - Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Consider for your loading time, switching with a TOP10LIST alternative WP Speed Plugin - OR - Hire professionals for managed WP Speed Up.
- Real Cookie Banner: GDPR (DSGVO) & ePrivacy Cookie Consent - Reflected Cross-Site Scripting (XSS)
- Active installations: 80.000+
- Consider for your online privacy, switching with a TOP10LIST alternative WP GDPR Plugin - OR - Hire professionals for managed WP GDPR.
- Easy Testimonials - Reflected Cross-Site Scripting (XSS)
- Active installations: 30.000+
- Checkout Field Manager (Checkout Manager) for WooCommerce - Reflected Cross-Site Scripting (XSS)
- Active installations: 90.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- WordPress Team Manager - Improper Access Control leading to multiple Authenticated Stored Cross-Site Scripting (XSS)
- WordPress Team Manager - Multiple Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 14, 2022 and is not available for download. This closure is temporary, pending a full review.
- ShortPixel Image Optimizer - Reflected Cross-Site Scripting (XSS)
- Active installations: 300.000+
- Consider for your online ranking, switching with a TOP10LIST alternative WP SEO Plugin - OR - Hire professionals for managed WP SEO.
- Table Rate Shipping Method for WooCommerce by Flexible Shipping - Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- Woody code snippets – Insert Header Footer Code, AdSense Ads - Reflected Cross-Site Scripting (XSS)
- Active installations: 80.000+
- Consider for your online vigilance, switching with a TOP10LIST alternative WP Monitoring Plugin - OR - Hire professionals for managed WP Monitoring.
- XO Slider - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 1.000+
- Popup Builder – Create highly converting, mobile friendly marketing popups. - Cross-Site Request Forgery (CSRF) leading to Popup Status Change
- Popup Builder – Create highly converting, mobile friendly marketing popups. - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 200.000+
- Button Widget Smartsoft - Cross-Site Request Forgery (CSRF) to Cross-Site Scripting (XSS)
- This plugin has been closed as of June 8, 2022 and is not available for download. This closure is temporary, pending a full review.
- CORE plugin for kitestudio themes - Reflected Cross-Site Scripting (XSS)
- Active installations: 2.000+
- Consider for your online safety, switching with a TOP10LIST alternative WordPress Themes - OR - Hire professionals for a Tailored WP Theme migration.
- WP-Paginate - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 40.000+
- Social Media Share Buttons | MashShare - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 30.000+
- pagebar - Arbitrary Settings Update via Cross-Site Request Forgery (CSRF) to Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 14, 2022 and is not available for download. This closure is temporary, pending a full review.
- Sharebar - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of June 14, 2022 and is not available for download. This closure is temporary, pending a full review.
- CDI – Collect and Deliver Interface for Woocommerce - Reflected Cross-Site Scripting (XSS)
- Active installations: 300+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- Import CSV Files - Reflected Cross-Site Scripting (XSS)
- This plugin has been closed as of June 16, 2022 and is not available for download. This closure is temporary, pending a full review.
- Consider for your online disaster recovery, switching with a TOP10LIST alternative WP Backup Plugin - OR - Hire professionals for managed WP Backup.
- XML Sitemaps - Stored Cross-Site Scripting (XSS)
- Active installations: 1+ million
- Consider for your online ranking, switching with a TOP10LIST alternative WP SEO Plugin - OR - Hire professionals for managed WP SEO.
- Ocean Extra - Reflected Cross-Site Scripting (XSS)
- Active installations: 800.000+
- Consider for your online safety, switching with a TOP10LIST alternative WordPress Themes - OR - Hire professionals for a Tailored WP Theme migration.
- WP Statistics - Stored Cross-Site Scripting (XSS)
- Active installations: 600.000+
- Consider for your online vigilance, switching with a TOP10LIST alternative WP Monitoring Plugin - OR - Hire professionals for managed WP Monitoring.
- Newsletter – Send awesome emails from WordPress - Stored Cross-Site Scripting (XSS)
- Active installations: 400.000+
- underConstruction - Stored Cross-Site Scripting (XSS)
- underConstruction - Construction Mode Deactivation via Cross-Site Request Forgery (CSRF)
- Active installations: 80.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Print, PDF, Email by PrintFriendly - Stored Cross-Site Scripting (XSS)
- Active installations: 40.000+
- Custom Share Buttons with Floating Sidebar - Stored Cross-Site Scripting (XSS)
- Active installations: 10.000+
- Post Grid, Slider & Carousel Ultimate - Stored Cross-Site Scripting (XSS)
- Active installations: 1.000+
- WP Zillow Review Slider - Stored Cross-Site Scripting (XSS)
- Active installations: 700+
- Inline Google Maps - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 23, 2022 and is not available for download. This closure is temporary, pending a full review.
- Multi-page Toolkit - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 23, 2022 and is not available for download. This closure is temporary, pending a full review.
- Login using WordPress Users (WP as SAML IDP) - Stored Cross-Site Scripting (XSS)
- Active installations: 700+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Ultimate WooCommerce CSV Importer - Reflected Cross-Site Scripting (XSS)
- This plugin has been closed as of May 16, 2022 and is not available for download. This closure is temporary, pending a full review.
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- WP Sentry - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 24, 2022 and is not available for download. This closure is temporary, pending a full review.
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Login With OTP Over SMS, Email, WhatsApp and Google Authenticator - Stored Cross-Site Scripting (XSS)
- Active installations: 100+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- OpenBook Book Data - Arbitrary Settings Update to Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of May 24, 2022 and is not available for download. This closure is temporary, pending a full review.
- Gallery – Image and Video Gallery with Thumbnails - Reflected Cross-Site Scripting (XSS)
- Active installations: 1.000+
- Analytify – Google Analytics Dashboard For WordPress - Reflected Cross-Site Scripting (XSS)
- Active installations: 60.000+
- Consider for your online ranking, switching with a TOP10LIST alternative WP SEO Plugin - OR - Hire professionals for managed WP SEO.
- Consider for your online vigilance, switching with a TOP10LIST alternative WP Monitoring Plugin - OR - Hire professionals for managed WP Monitoring.
- DX Share Selection - Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- Active installations: 10+
- LiveSupporti - Free Live Chat Support - Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- Active installations: 3.000+
- Data Tables Generator by Supsystic - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 30.000+
- Loading Page with Loading Screen - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 10.000+
- Page Generator - Authenticated Stored Cross-Site Scripting (XSS)
- Page Generator - Arbitrary Keywords Deletion/Duplication via Cross-Site Request Forgery (CSRF)
- Active installations: 3.000+
- Simple Post Notes - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 9.000+
- Accept Stripe Payments - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 40.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Discount Rules for WooCommerce - Reflected Cross-Site Scripting (XSS)
- Active installations: 90.000+
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- Advanced Database Cleaner - Reflected Cross-Site Scripting (XSS)
- Active installations: 90.000+
- Contact Form 7 Captcha - Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Request a Quote - CSV Injection
- Request a Quote - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 21, 2022 and is not available for download. This closure is temporary, pending a full review.
- W-DALIL - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 28, 2022 and is not available for download. This closure is temporary, pending a full review.
- Simple Page Transition - Authenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 28, 2022 and is not available for download. This closure is temporary, pending a full review.
- WP Maintenance - Authenticated Stored Cross-Site Scripting (XSS)
- Active installations: 30.000+
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- WordPress Popular Posts - Reflected Cross-Site Scripting (XSS)
- Active installations: 200.000+
- FoxyShop - Reflected Cross-Site Scripting (XSS)
- This plugin has been closed as of June 2, 2022 and is not available for download. This closure is temporary, pending a full review.
- Awin Data Feed - Reflected Cross-Site Scripting (XSS)
- Awin Data Feed - Unauthenticated Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 10, 2022 and is not available for download. This closure is temporary, pending a full review.
- Consider for your online safety, switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for managed WP Security.
- Popup | Custom Popup Builder - Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of May 26, 2022 and is not available for download. This closure is temporary, pending a full review.
- WooCommerce – Product Importer - Reflected Cross-Site Scripting (XSS)
- This plugin has been closed as of June 2, 2022 and is not available for download. This closure is temporary, pending a full review.
- Consider for your online shop, switching with a TOP10LIST alternative WooCommerce Plugin - OR - Hire professionals for managed WooCommerce.
- Travel Management - Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of May 6, 2022 and is not available for download. This closure is temporary, pending a full review.
- LearnPress – WordPress LMS Plugin - Reflected Cross-Site Scripting (XSS)
- Active installations: 100.000+
- Brizy – Page Builder - Stored Cross-Site Scripting (XSS) via Element URL
- Brizy – Page Builder - Stored Cross-Site Scripting (XSS) via Element Content
- Active installations: 90.000+
- 404s - Stored Cross-Site Scripting (XSS)
- Active installations: 10+
- LinkedIn Company Updates - Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 21, 2022 and is not available for download. This closure is temporary, pending a full review.
- Very Simple Breadcrumb - Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 21, 2022 and is not available for download. This closure is temporary, pending a full review.
- Free Live Chat Support - Stored Cross-Site Scripting (XSS) via Cross-Site Request Forgery (CSRF)
- This plugin has been closed as of June 14, 2022 and is not available for download. This closure is temporary, pending a full review.
- Best Contact Management Software for WordPress - Stored Cross-Site Scripting (XSS)
- This plugin has been closed as of June 21, 2022 and is not available for download. This closure is temporary, pending a full review.
Stay Healthy! A healthier online business starts today and it begins with your WP/Woo. Hire security experts to solve all your XSS JUL 2022 issues.
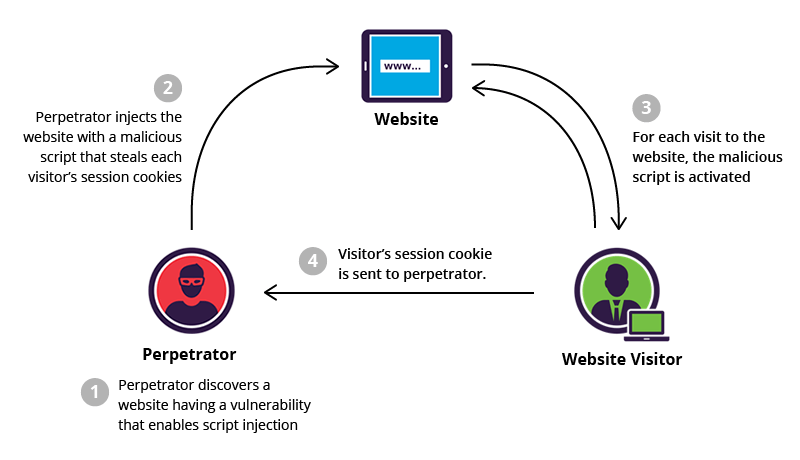
BRIEF: Cross-Site Scripting JUL 2022 is a type of security vulnerability typically found in web applications. XSS attacks enable attackers to inject client-side scripts into web pages viewed by other users. A cross-site scripting vulnerability may be used by attackers to bypass access controls such as the same-origin policy.
What is Cross-Site Scripting JUL 2022?
Cross-Site Scripting (XSS) attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws that allow these attacks to succeed are quite widespread and occur anywhere a web application uses input from a user within the output it generates without validating or encoding it.
An attacker can use XSS to send a malicious script to an unsuspecting user. The end user’s browser has no way to know that the script should not be trusted, and will execute the script. Because it thinks the script came from a trusted source, the malicious script can access any cookies, session tokens, or other sensitive information retained by the browser and used with that site. These scripts can even rewrite the content of the HTML page.
What is the impact of a XSS JUL 2022 attack?
The actual impact of an XSS attack generally depends on the nature of the application, its functionality and data, and the status of the compromised user. For example:
- In a simple public application, where all users are anonymous and all information is public, the impact will often be minimal. Nothing else to steal.
- In an application holding sensitive or private/personal data, such as banking transactions, emails, or healthcare records, the impact will usually be serious.
- If the compromised user has elevated privileges within the application, then the impact will generally be critical, allowing the attacker to take full control of the vulnerable application and compromise all users, owners and their data.
What kind of XSS attacks are exploited?
- Reflected XSS, where the malicious script comes from the current HTTP request.
- Stored XSS, where the malicious script comes from the website's database.
- DOM-based XSS, where the vulnerability exists in client-side code rather than server-side code.
SOLVE TODAY any reported XSS JUL 2022 vulnerability! Do you suspect any Cross-Site Scripting JUL 2022 in your WordPress / WooCommerce?