SSRF JUL 2023
Server-Side Request Forgery JUL 2023
Tailored Woo/WP Security Report
Be informed about the latest Server-Side Request Forgery JUL 2023, identified and reported publicly. As these SSRF JUL 2023 vulnerabilities have a severe negative impact on any WordPress Security, consider our security audit.
It is a +67% INCREASE compared to previous month, as specifically targeted Server-Side Request Forgeries. Consider for your online safety, a tailored WP/Woo Security AUDIT, - OR - switching with a TOP10LIST alternative WP Security Plugin - OR - Hire professionals for tailored WP Security.
The following cases made headlines PUBLICLY in the SSRF JUL 2023 & Server-Side Request Forgery JUL 2023 category:
Hire security geeks to protect your WP/Woo from publicly reported cases of SSRF JUL 2023 BEFORE IT'S TOO LATE! You will also protect your customers, your reputation and your online business!
| Download Monitor | Server-Side Request Forgery (SSRF) |
| Getwid – Gutenberg Blocks | Server-Side Request Forgery (SSRF) |
| Poll Maker | Server-Side Request Forgery (SSRF) |
| wpForo Forum | Server-Side Request Forgery (SSRF) |
| WPGraphQL | Server-Side Request Forgery (SSRF) |
| SSRF & Server-Side Request Forgery reported in 2023 so far | 27 |
Stay Healthy! A healthier online business starts today and it begins with your WP/Woo. Hire security experts to solve all your SSRF JUL 2023 issues.
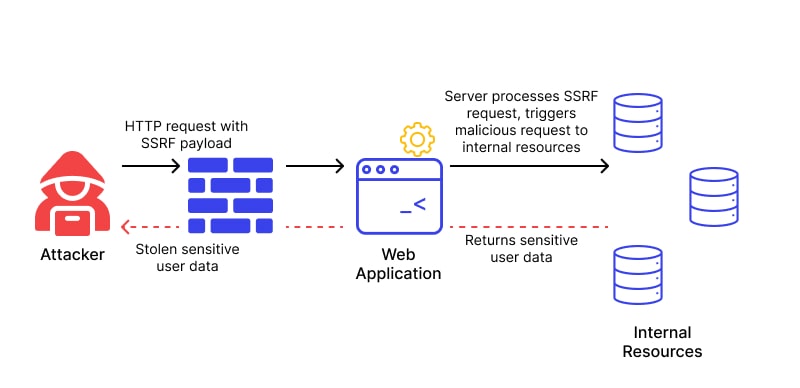
BRIEF: Server-Side Request Forgery JUL 2023 is a type of hosting server security exploit, where an attacker abuses the basic functionality of a hosting environment, causing it to access or manipulate information in the realm of that server that would otherwise not be directly accessible to the attacker.
What is Server-Side Request Forgery JUL 2023?
Server-Side request forgery (also known as SSRF) occur whenever a WordPress or WooCommerce is fetching a remote resource without validating the user-supplied URL. It allows an attacker to coerce the public side (front-end) to send a crafted request to an unexpected destination (back-end, database, files), even when protected by a firewall, or another type of network access control list (ACL).
As modern websites provide end-users with convenient features, fetching an URL becomes a common tactic. As a result, the incidence of SSRF 2023 is increasing. Also, the severity of SSRF 2023 is growing higher due to publicly accessible cloud services and the complexity of their architectures.
What is the impact of a SSRF JUL 2023 attack?
A successful SSRF 2023 attack can often result in unauthorized actions on the hosting environment or access to data within WordPress and WooCommerce, or on other back-end systems that the application can communicate with like database or 3rd party integrations (payment modules, seo modules, marketing modules, analytics modules, etc). In some situations, the SSRF vulnerability might allow an attacker to perform arbitrary command execution, compromising everything.
A specific and successful SSRF 2023 exploit that causes connections to external systems, always generates malicious direct attacks, that appear to originate from the domain itself or hosting environment, continuing its attack towards the next vulnerable external system.
SOLVE TODAY any reported SSRF JUL 2023 vulnerability! Do you suspect any Server-Side Request Forgery JUL 2023 in your Woo/WP?